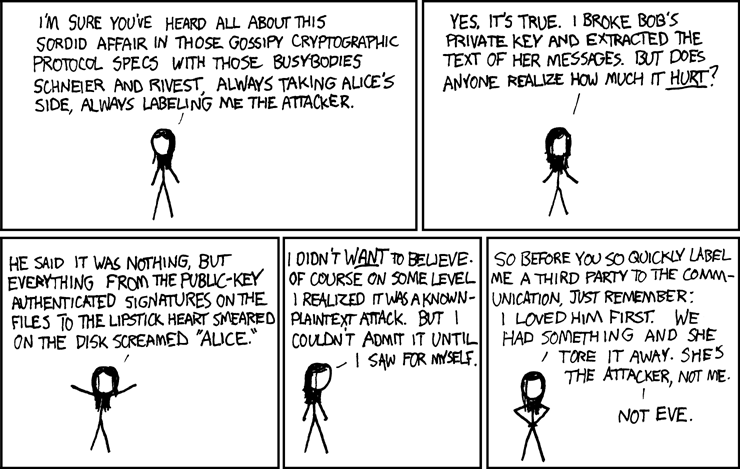
Alice and Bob are the example names regularly used in explanations and discussions of public key cryptography. "Eve, an eavesdropper, is usually a passive attacker. While she can listen in on messages between Alice and Bob, she cannot modify them." These two have been the talk of the geekosphere for quite a while now.
Stumbled on this via tabo @ aureal.
No comments:
Post a Comment